What is new in Android N? Lots of new changes: APIs, power management, related to notifications, new multi-window UI, permissions, Graphics APIs, other… 1. Android 7.0 -> API Level 24. 2. API differences: https://developer.android.com/sdk/api_diff/24/changes.html 3. Behavioral differences: https://developer.android.com/about/versions/nougat/android-7.0-changes.html 4. General overview: https://www.android.com/versions/nougat-7-0/ 5.…
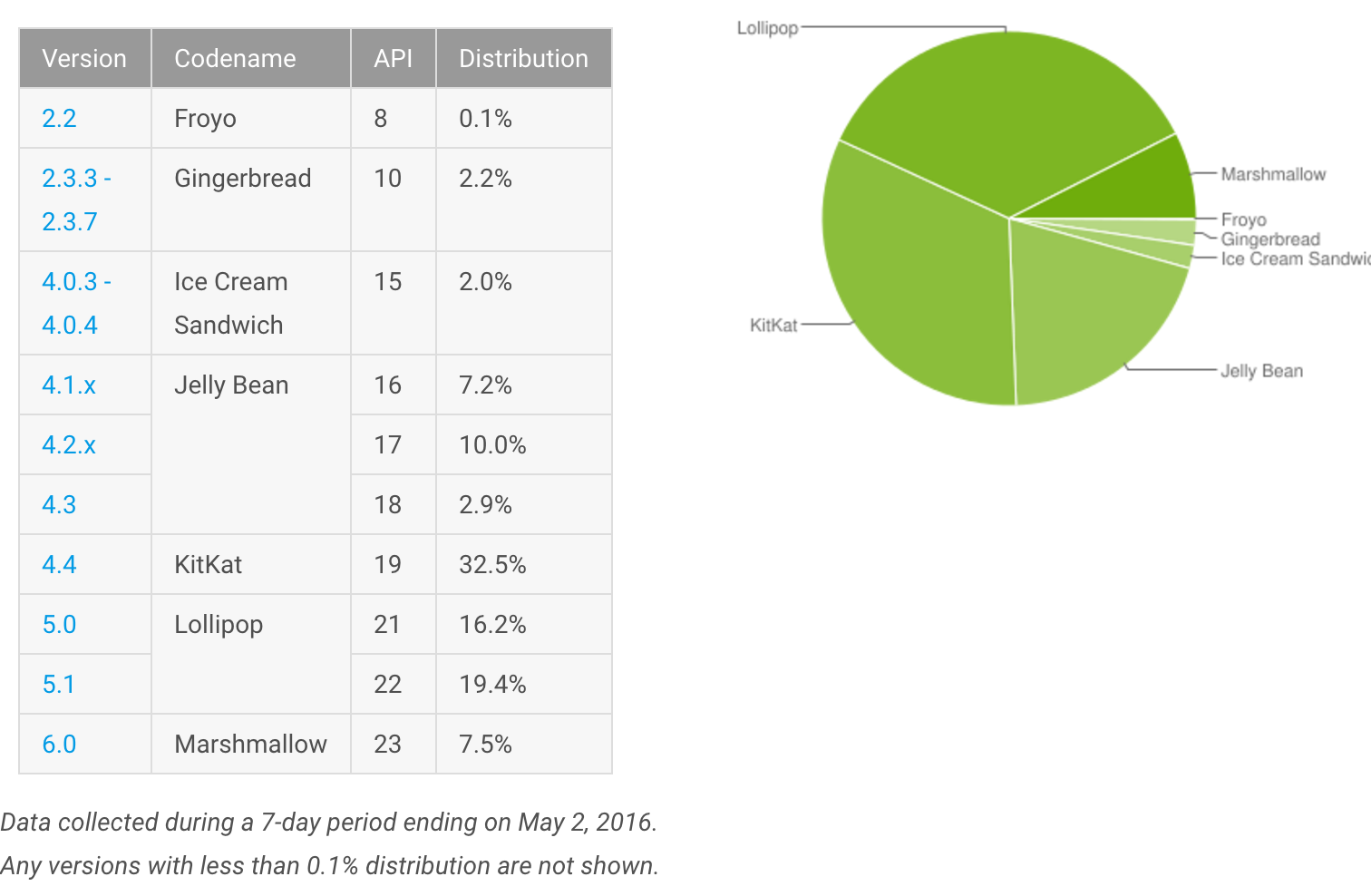
Every year I like to take a snapshot of the Android platforms adoption. It is great to compare Year-to-Year numbers for historical purposes. Keeping track of platform adoption is important as it directly impacts what developers should be focusing on vs. what should…
Due to its origins and philosophy with respect to openness, Android is a fragmented mobile platform. This is illustrated next: There are different kinds of fragmentation to keep in mind. Android platform versions. To minimize fragmentation-related headaches, decide early on what versions of…
I wrote a small piece for the Safari Flow Blog: With sales of Android devices growing, there’s no better time to get started crafting your first Android app. Here are the five things you need to know before creating that first killer app.…
My most recent piece is about Using Android’s Advertising ID (Safari Online Books blog). The ability to identify users is important for advertising, analytics and other purposes. Android developers typically rely on the Android Device ID or Telephony IDs such as the International…
Check out the new guest post that I wrote on Android 4.4, for the Safari Books Online blog. It summarizes what is new on Android and related important information. In this post we will explore the major changes introduced in Android 4.4. Android…
Nice… I just received a copy of Android in Action 3rd edition, which I co-authored, translated to Portuguese! (I would like to learn Portuguese.) ceo
Below is a snapshot of the Android platform distribution, as of September 2012. As you can see, the majority of the devices out there, close to 60%, are still 2.3 (Gingerbread). This is followed by ICS with close to 21%. Froyo 2.2 is…
Write Facebook apps for the Android platform with the Facebook Android SDK… You can incorporate Facebook functionality into your own applications. From the mobile perspective, the Facebook Platform supports APIs for mobile web applications, and mobile SDKs for native mobile applications for the…